What is Authentication Used For?
Authentication and secure identity are two closely related requirements for digital recognition systems. The purpose of authentication is to ensure that only authorized persons or systems can access protected areas. Authentication is used as soon as the unique recognition of an identity or system is necessary in order to reliably rule out mix-ups or forgeries. Object identification, like product identification, for example, also requires authentication.
In simple terms, authentication secures the identity of a user and verifies that it is actually the claimed identity. After verification, the user receives authorization or, in other words, the access authorization to perform the desired action. Machine authentication, for example, ensures that only authorized employees are able to access and operate certain machines. Authentication methods secure systems and data. They make unauthorized access more difficult. Different authentication methods are used depending on the security level. Risk guidelines help to evaluate methods.
Methods of Authentication
With password-based authentication services, the user enters a password or a secret phrase that is linked to their user account and is used for verification. The system then checks whether the password entered matches the stored password. Password hashing and salting techniques are used to increase the security of passwords. Other authentication methods are also possible.
Biometric Authentication
What is biometric authentication? Biometric identification includes fingerprints, facial scans, hand geometry, iris scans, or voice. These biometric identifiers are unique and difficult or impossible to forge. They are also used for authentication.
Virtual Tokens
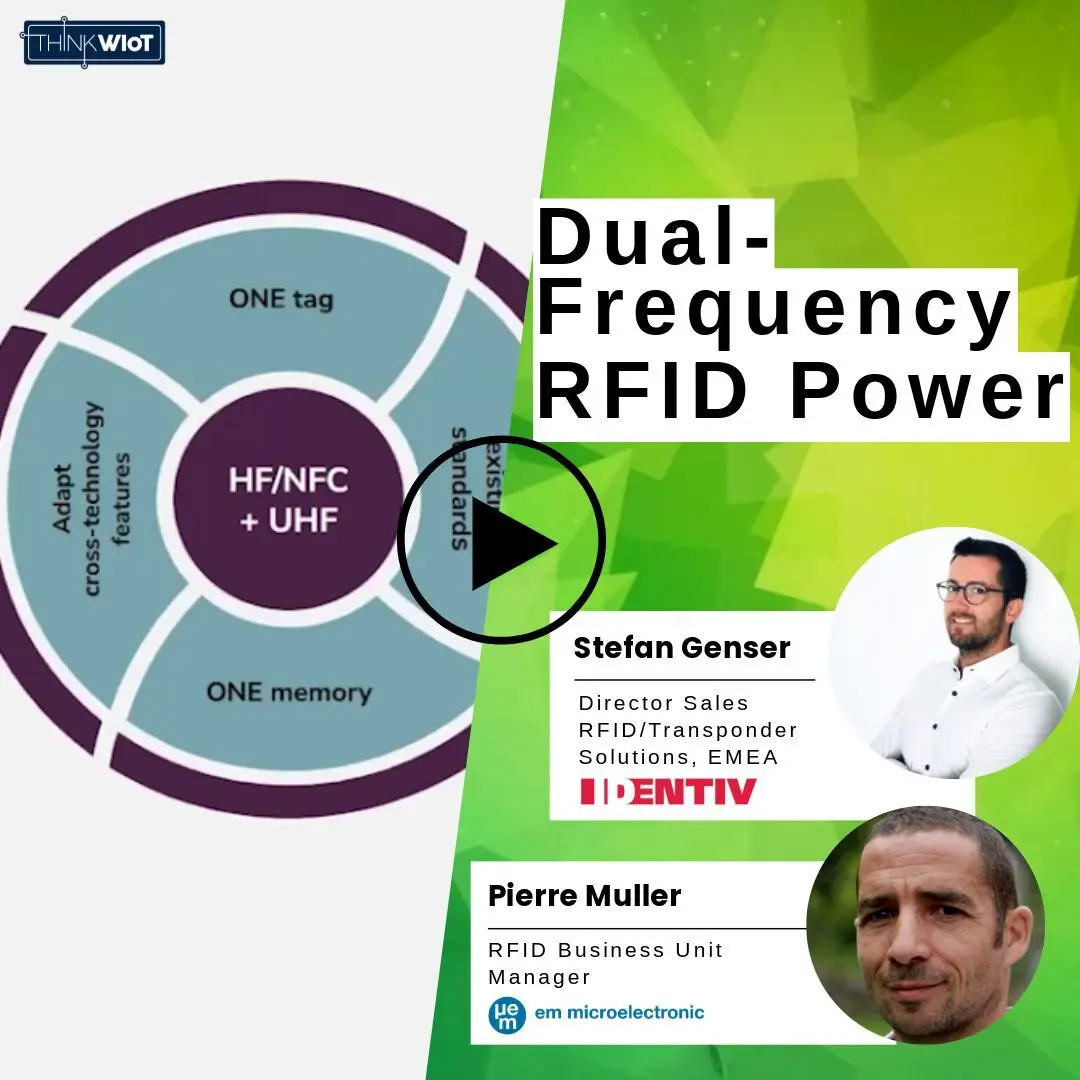
Token-based authentication with smartcards, RFID chip cards, or one-time passwords uses physical or virtual tokens to confirm identity.
Two-Factor Authentication (2FA)
Two-factor authentication (2FA) combines two authentication components. These could be a password and a one-time token code sent by SMS, for example. If multi-factor authentication (MFA) is used, three authentication components are used to confirm the identity of a user. The Single Sign-On (SSO) method allows users to log in to multiple related applications or services with just one set of credentials. The use of SSO increases convenience for the user as the login process is streamlined.
Fast Identity Online (FIDO)
The authentication standard specification FIDO aims to reduce dependence on passwords and enable stronger authentication. FIDO supports various authentication methods such as biometrics, tokens, and public key encryption. Blockchain-based authentication can be used to improve the security and integrity of identity, and authentication processes in the Internet of Things (IoT). By using blockchain, proof of identity can be stored securely and immutably, reducing the risk of identity theft and forgery. A good example of a counterfeit protection measure.
Central Management of Authorizations
For complex IoT environments, identity and access management platforms can be used to centralize and manage the authentication and authorization of users and devices. These platforms offer functions such as user and device authentication, access control, identity federation, and single sign-on.
Wireless IoT Technologies and Authentication
Which Products Are Used for Authentication?
Products or technologies for authentication are often combined with each other. This increases the level of security and, in some cases, convenience. Smart cards are common components for authentication. They normally require a PIN to be entered or biometric confirmation, and communicate with a stationary or mobile wireless RFID reader. In addition to writing and reading units, biometric scanners are used to capture a person's physiological characteristics. These include fingerprints, hand geometry, face, iris, or even the voice.
Access control systems and gates are often used in companies, public institutions and airports to control access to certain areas or resources.
Token generators are devices or applications that generate one-time passwords or token codes that are used for authentication. These codes can be physical (for example as a hardware token) or virtual (for example as a mobile app) and serve as an additional authentication factor alongside a password or other method. Mobile devices such as smartphones and tablets can also be used for authentication, especially with biometric sensors such as fingerprint scanners or facial recognition. Mobile apps can also be used as token generators or to perform authentication processes via a secure connection.
In Which Industries Does Authentication Take Place?
Authentication solutions with different security levels and methods must be used in a variety of industries to verify the identity of users, devices, or systems. When it comes to secure access to systems, such as in IT, finance, healthcare, government, aerospace, military, or industry, access to networks, control systems, and databases must be secured. Users must identify themselves using authentication methods with different levels of security in order to access systems or applications. Only once authentication has been successful can the user carry out transactions, view databases, or access medical files.
This primarily involves sensitive data that may only be made accessible to authorized persons or systems. In the aerospace industry, for example, security is of crucial importance. Here, authentication plays an important role in controlling access to aircraft, airports, and air traffic control systems. In the defense and military sectors, authentication is used to control access to top secret information, military systems, and facilities. This can include highly secure authentication methods such as biometrics and smart cards. In industry, industrial control systems (ICS) and production systems in particular, need to be protected against unauthorized access.
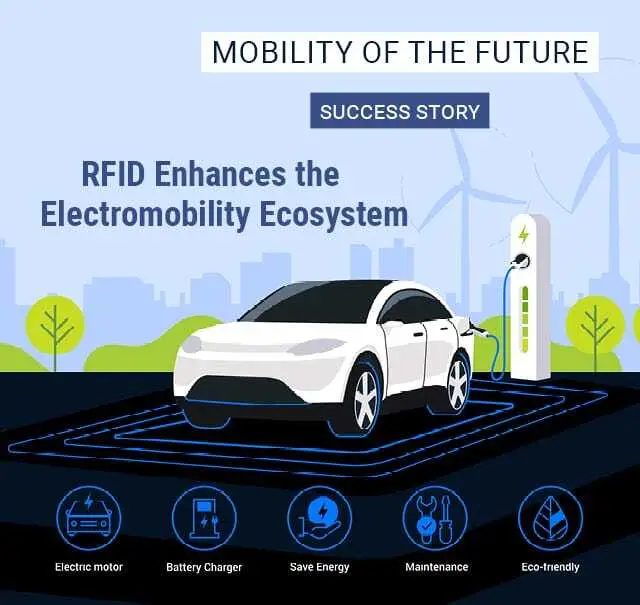
In addition to personal authentication, other security scenarios are also possible. For example, with increasing digitalization in the automotive industry, RFID is being used for industrial identification. This includes applications like vehicle identification and authentication. In other applications, goods must also be authenticated before they are approved as components or parts for production. The aim is to verify authenticity and prevent the installation of counterfeit components.
Facts & Figures
The rising rates of identity theft and online fraud contributes to the increase in demand for authentication solutions. According to a report by the market intelligence and advisory firm “Mordor Intelligence”, multifactor authentication is being used as a countermeasure against data breaches. In 2017, 81 percent of cyberattacks around the world were the result of insecure passwords.
According to a report by the Canadian-Indian market insights provider “Precedence Research”, the password authentication segment had the largest share of the global market for multi-factor authentication in 2023 at 57 percent. Within this market, the multi-factor with three-factor authentication segment had a share of more than 29 percent in 2023. Over 45 percent of the global market share was generated by the hardware segment for authentication solutions in 2023.
Real-World Authentication Examples
Authentication solutions are in use in many different industries worldwide. The following success stories show the different authentication solutions that are in use in payment, digitalized traffic, and laundry management, for example. What kind of technologies were chosen for each application? These solutions, based on real-world success stories, show what can be made possible with authentication.
Authentication Solutions from Copecto

In July 2023, the start-up Copecto introduced the world's first plastic-free wooden payment card, the Timbercard. Holding a global license for its distribution and production, Copecto delegated the industrialized production of these wooden cards to the PCI and FSC-certified card manufacturer, Raiffeisendruckerei.
The Timbercard, made from certified regional woods and paper layers bound with biodegradable adhesive, stands out for the complete absence of plastic. Only the chip, antenna, and magnetic stripe are non-biodegradable. The embedding of an RFID or NFC chip is possible for applications in contactless payment, authentication, or access control. The card meets stringent international standards without compromising on durability or functionality.
In July 2023, the start-up Copecto introduced the world's first plastic-free wooden payment card, the Timbercard. Holding a global license for its distribution and production, Copecto delegated the industrialized production of these wooden cards to the PCI and FSC-certified card manufacturer, Raiffeisendruckerei.
The Timbercard, made from certified regional woods and paper layers bound with biodegradable adhesive, stands out for the complete absence of plastic. Only the chip, antenna, and magnetic stripe are non-biodegradable. The embedding of an RFID or NFC chip is possible for applications in contactless payment, authentication, or access control. The card meets stringent international standards without compromising on durability or functionality.

"At the specific request of the GLS Bank to obtain a payment card made purely from natural and renewable materials in addition to the antenna, magnetic strip and chip, we started production in 2022 in the style of a manufactory with a lot of manual work. We are currently working on mass-producing the Timbercard with the new machinery. At the same time, we are researching further Timbercard innovations with our partners in order to meet current and future customer requirements. This year, it is all the more gratifying to see the work of our entire team honored with the TOP 100 seal as one of the 100 most innovative medium-sized companies in Germany.”

Claudius Pawliczek
Division Manager/Procurator Products & Operations
Authentication at NMBS/SNCB

In the central workshop of the Belgian railroad company NMBS/SNCB in Mechelen, electronic components are tested for their functionality. These include wheelsets, brake controllers, control valves, AC3D boxes and weighing valves. High-voltage tests are also permitted in the new test laboratory, as the train converters have to be tested at 3,000 volts after a repair. When the voltage is switched off, charge can still be present in coils and capacitors. Access to the rooms where the 3000-volt tests are carried out is therefore only permitted to authorized employees. The access door is RFID-secured. The RFID system used is supplied by Turck.
In the central workshop of the Belgian railroad company NMBS/SNCB in Mechelen, electronic components are tested for their functionality. These include wheelsets, brake controllers, control valves, AC3D boxes and weighing valves. High-voltage tests are also permitted in the new test laboratory, as the train converters have to be tested at 3,000 volts after a repair. When the voltage is switched off, charge can still be present in coils and capacitors. Access to the rooms where the 3000-volt tests are carried out is therefore only permitted to authorized employees. The access door is RFID-secured. The RFID system used is supplied by Turck.

"The converter tests must be carried out in accordance with strictly regulated procedures under the highest safety precautions. The risks of a 3000 volt installation should not be underestimated. Even when the voltage is switched off, charge may still be present in coils and capacitors. Therefore, the work must always be carried out systematically, according to established procedures and by authorized persons who are aware of the risks."

Kristof Honee
Head of electronic repair workshop NMBS Mechelen
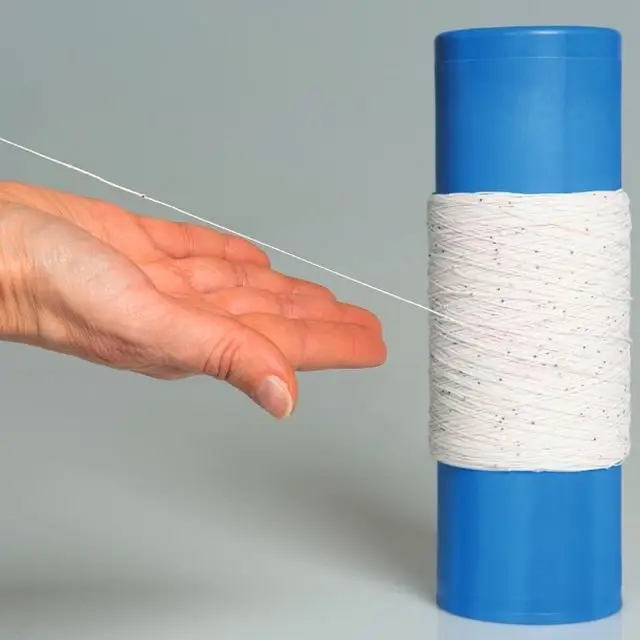
Authentication at Nordland Hospital

In 2021, the Nordland Hospital in Norway implemented a central room solution for laundry management based on RFID technology. Over 30,000 items of clothing at the hospital are equipped with a sewn-in UHF RFID inlay that can withstand over 200 wash cycles. With the RFID room solution from Deister Electronic, only authenticated employees can remove the clothes. Each employee can take a maximum of 6 items of laundry with them. Borrowed laundry items must be returned via return lockers before new laundry items can be removed.
The textile management solution enables fast authentication and registration of employees and ensures that sufficient clean laundry is available around the clock.
In 2021, the Nordland Hospital in Norway implemented a central room solution for laundry management based on RFID technology. Over 30,000 items of clothing at the hospital are equipped with a sewn-in UHF RFID inlay that can withstand over 200 wash cycles. With the RFID room solution from Deister Electronic, only authenticated employees can remove the clothes. Each employee can take a maximum of 6 items of laundry with them. Borrowed laundry items must be returned via return lockers before new laundry items can be removed.
The textile management solution enables fast authentication and registration of employees and ensures that sufficient clean laundry is available around the clock.

“The new solution benefits everyone: the patients, the employees, hygiene, the environment and – through the cost reduction – also the clinic’s management.”

Vibeke Mikalsen
Head of Operations
More Stories on Authentication
The Future of IoT and Mobile Identities
The world is changing. While a person's identity used to be tied to a haptic ID document, many smartphone owners now use digital IDs. Since almost everyone has a mobile device, it has become an integral part of everyday life. The original function of 'making phone calls' has been relegated to a secondary function. Today, numerous use cases are associated with the smartphone. These include payment, managing contacts and appointments, generating information, research, and even digital identification. Behind the digital ID card is the driver's license, the personal identity card, the health insurance card, or even the employee ID card.
Storing a digitalized bank card on the smartphone and then paying with the mobile phone? What sounded adventurous a few years ago has long since become reality. Digital wallets are paving the way to a society without cash and bank cards.
These mobile identities are practical because most people always have their mobile device on hand. However, there are also hurdles to their use. These include authentication, data protection, and infrastructure availability. This applies, for example, to medical practices, canteens, or company areas.
Overall, acceptance of mobile identities is increasing. The growing infrastructure is also a driver for mobile identities. With the increase in mobile identities, the number of plastic cards is also decreasing. Less plastic also means less CO2 emissions. In the university sector, students can already use their mobile ID cards for numerous applications. For example, opening doors, borrowing books, operating equipment, or paying for lunch in the canteen. Universities are pioneers in the 'mobile-first approach'.
Partners Spezialized in Authentication Solutions
Advantages of Authentication
Advantages of Wireless IoT
- High security level
- Authorized access to systems
- Securing high-security areas
- A combination of different methods
- Convenient use
The biggest advantage of authentication lies in securing systems. Access to numerous buildings, offices, computer systems, databases, or machines can, and is, secured in this day and age via authorized access. First and foremost, this means that only people who are authorized, are granted access. Users identify themselves via an authentication system. In this way, it can be ensured that only certain people gain access to data, control elements, functional areas, or computer systems. Another major advantage is data protection for companies, as only authorized users can gain access to sensitive data. This ensures the protection of privacy or confidential information.
Another advantage is the prevention of unauthorized access to systems or data. Authentication methods use passwords, biometric features, or two-factor authentications to ensure that the identity seeking access to systems is secure. This ensures that users are actually who they say they are.
The documentation of authentication also makes it possible to audit all activities. It is possible to track exactly which user entered the system, the database, or the room and when.
Today, certain industries, legal regulations, and data protection regulations require strong authentication to ensure the security of sensitive information and systems. By implementing appropriate authentication methods, organizations can meet regulatory requirements and ensure compliance.
The biggest advantage of authentication lies in securing systems. Access to numerous buildings, offices, computer systems, databases, or machines can, and is, secured in this day and age via authorized access. First and foremost, this means that only people who are authorized, are granted access. Users identify themselves via an authentication system. In this way, it can be ensured that only certain people gain access to data, control elements, functional areas, or computer systems. Another major advantage is data protection for companies, as only authorized users can gain access to sensitive data. This ensures the protection of privacy or confidential information.
Another advantage is the prevention of unauthorized access to systems or data. Authentication methods use passwords, biometric features, or two-factor authentications to ensure that the identity seeking access to systems is secure. This ensures that users are actually who they say they are.
The documentation of authentication also makes it possible to audit all activities. It is possible to track exactly which user entered the system, the database, or the room and when.
Today, certain industries, legal regulations, and data protection regulations require strong authentication to ensure the security of sensitive information and systems. By implementing appropriate authentication methods, organizations can meet regulatory requirements and ensure compliance.
Advantages of Wireless IoT
- High security level
- Authorized access to systems
- Securing high-security areas
- A combination of different methods
- Convenient use
Challenges: Data Leakage Through Man-in-the-Middle Attacks
In addition to the numerous advantages, the integration of authentication methods also presents companies and institutions with challenges. Digitalization for companies results in the growing use of growing use of networked devices. This means that authentication methods must meet increasing levels of security. Large companies or institutions in particular, are forced to develop scalable solutions for security strategies.
A large number of users, computer systems, or machines involved require prudent planning of security strategies. Changing legal requirements also present companies with the challenge of adapting authentication methods or security strategies. Known attack scenarios include man-in-the-middle attacks or denial-of-service attacks. These can lead to data leaks or security breaches. These attacks make it clear how important authentication solutions are. For example, passwords, even if they are one of the most common authentication solutions, are susceptible to misuse. Vulnerabilities such as brute force attacks, phishing and dictionary attacks are not uncommon.
Biometric data is far more secure than passwords. However, they are not immune to forgery either. On the one hand, authentication solutions should be user-friendly, but on the other hand, they should also offer maximum security. These two requirements are not always easy to reconcile. The challenge is to find a compromise between security and user-friendliness.
The Dangers of Identity Theft
Secure authentication always assumes that the user is actually the bearer of the identity. If identity theft occurs, attackers can take advantage of this stolen identity by attempting to access systems, databases, accounts, or networks. Forged identities can be used, for example, to carry out financial transactions, open accounts, or pass on fraudulent information.
The misuse of authentication is therefore based on the misuse of an identity and, secondly, access to unauthorized systems. This can result in financial loss, damage to reputation, loss of trust in systems, and faulty networks. Efficient security measures and authentication technologies are essential to make access to systems more difficult in the event of falsified identities. This is possible when secure passwords are combined with multi-factor authentication.
What is Biometric Authentication?
With biometric authentication, the wearer himself is the security feature. Their biometric data serves as unique proof of their identity. This includes, for example, the fingerprint, the iris or retina of the eyes, the voice, or facial recognition. Even the geometry of the hand or the way a person walks and moves can be unmistakable characteristics of an individual. Biometric authentication is therefore a method of identity verification based on a person's physiological or behavioral characteristics.
Unlike traditional authentication methods such as passwords or tokens, which require knowing something (like a password) or possessing something (like a token), biometric features are extremely secure and therefore also offer many advantages. This is mainly due to the fact that biometric features are difficult to forge. At the same time, they are user-friendly as they are worn on the body, so to speak, and are automatically available at all times. For this reason, biometric authentication methods are characterized by speed and efficiency.