- NIS2 extends cybersecurity obligations to a wider range of sectors including industrial and logistics providers.
- The directive mandates integrated security across device, edge, and platform layers rather than isolated measures.
- Trusted device identity, firmware integrity, secure wireless communication, and segmented architectures are essential compliance elements.
- Responsibility for cybersecurity is anchored at management level and encompasses the full supply chain.
The European NIS2 Directive (EU) 2022/2555 shifts cybersecurity from an IT task to an enterprise-wide obligation. NIS stands for Network and Information Security. NIS2 is the successor to the first NIS Directive of 2016, which first defined EU-wide minimum requirements for cybersecurity but primarily concerned traditional critical infrastructure.
NIS2 significantly expands this framework. The directive was adopted in 2022 and has been in force since January 2023. EU member states were required to transpose it into national law by October 2024. In practice, however, the picture is mixed: some countries implemented the requirements on time, while others, including Germany, followed suit later.
For companies, this means a high degree of urgency. The requirements are already in effect or are imminent, while at the same time there is uncertainty regarding detailed national regulations. The designation 2022/2555 refers to the year of adoption and the serial number of the EU directive.
For providers and operators of IoT systems, this creates a new reality: connected devices, wireless technologies, and platforms are becoming part of regulated infrastructures.
More affected companies, higher requirements
NIS2 extends the scope far beyond traditional critical infrastructure. Industrial companies, logistics service providers, and digital platform operators now also fall under the regulation.
This puts IoT systems at the center. Production facilities, connected sensors, and digital supply chains are no longer just drivers of efficiency, but security-relevant systems. Companies must view their entire technical architecture through the lens of cyber resilience.
Security becomes a feature of the architecture
A central element of the directive is mandatory cyber risk management. Crucially, security can no longer be implemented in isolated areas. It must be effective across the entire system architecture, from the device level to the backend.
For IoT, this represents a clear shift: edge devices, wireless communication, and platforms must be secured as a cohesive system. Individual measures are insufficient if the data chain as a whole remains vulnerable.
Specific measures for wireless IoT and edge systems
For wireless IoT systems, NIS2 is particularly relevant where devices, radio links, gateways, and platforms are permanently integrated into operational processes.
What matters is not just whether a single device communicates using encryption. What matters is whether the entire architecture is identifiable, controllable, monitorable, and maintainable.
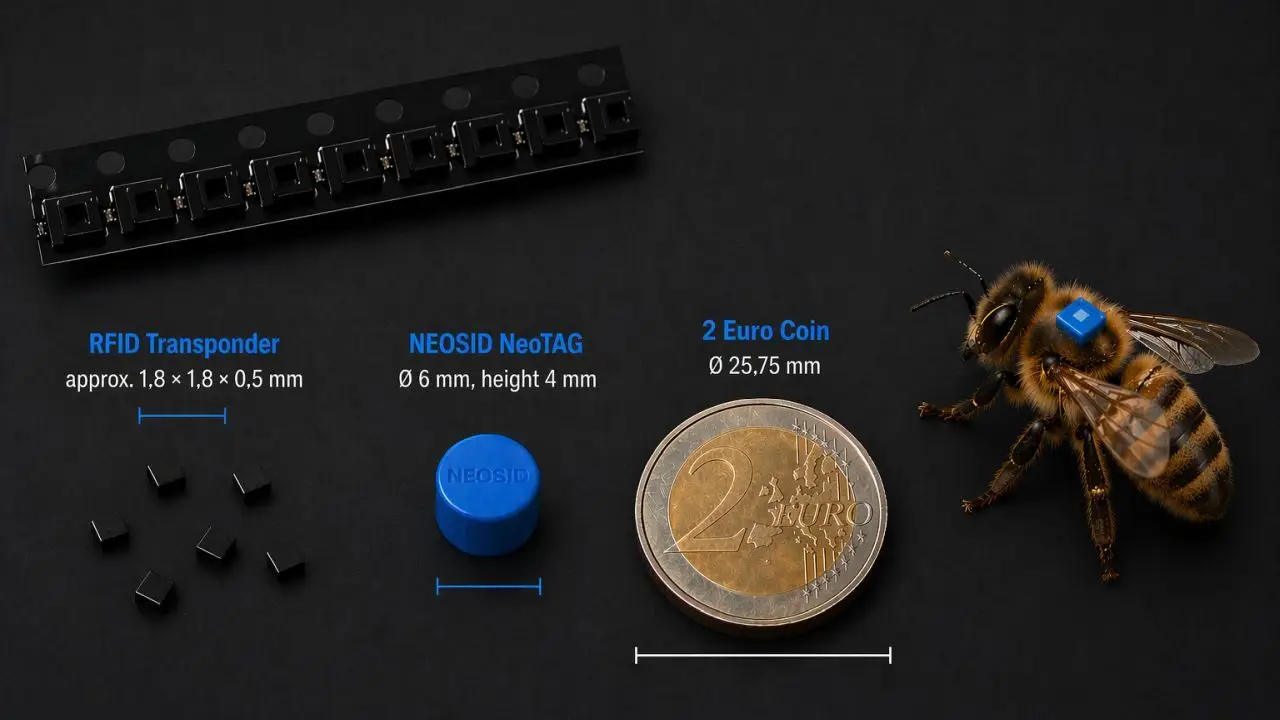
At the device level, this begins with a trusted identity. Sensors, tags, gateways, and edge devices must be uniquely identifiable. For active IoT devices, this can be achieved through certificates, secure elements, or comparable mechanisms. For passive technologies such as RFID, the focus is more on the controlled reader infrastructure, the secure mapping of tag data, and the protection of the middleware.
Equally critical is firmware integrity. Edge devices, gateways, and active sensors should only run trusted software. Secure boot, signed firmware, and secure update processes are key technical foundations for this. Especially for devices with long lifecycles, security must not end with the initial rollout. Updates, key rotation, and device management must remain possible over the years.
Wireless communication itself must be secured against tampering, spoofing, and replay attacks. For LoRaWAN, this involves key management and secure device activation. For BLE and RTLS systems, the focus is on beacon authentication and the integrity of location data. For cellular or 5G-based IoT connections, secure network profiles and controlled connections to the backend are added.
Gateways are becoming security-critical nodes. They must be hardened, regularly updated, and operated in isolation from the rest of the network. At the same time, clear network segmentation is necessary to separate IoT systems from IT and OT domains and prevent lateral attacks.
Edge systems are increasingly taking on active security functions. They can detect anomalies, secure data locally, and continue operating independently in the event of a failure. This makes them a central building block for resilient real-time systems.
The platform level is also becoming subject to regulatory requirements. Companies must be able to track at all times which devices are active, how they are configured, and who is accessing data. Centralized device management, auditability, and secure interfaces are necessary for this.
The IoT Edge-Cloud Continuum as a Security Architecture
Against this backdrop, the concept of the IoT edge-cloud continuum is gaining importance. It describes an architecture in which data processing and intelligence are distributed across devices, edge components, and cloud systems.
In the context of NIS2, this continuum serves as a blueprint for resilient systems. Security functions must be implemented along this entire chain. This begins with the secure identity of a device, continues with protected wireless communication, and ends with controlled processing in the cloud.
A key advantage of this architecture lies in the distribution of responsibility. Edge systems can make security-related decisions locally, while central platforms handle overarching monitoring and control.
Reporting Requirements and Operational Implementation
In addition to technical requirements, NIS2 mandates clear processes for handling security incidents. Events must be detected, assessed, and reported early on.
For IoT systems, this means that data from devices, networks, and platforms must be consolidated. Only in this way can incidents be reliably detected and the required response times met.
Responsibility and supply chains
NIS2 anchors cybersecurity at the management level and encompasses the entire supply chain. Companies must be able to track which components and services are used in their systems and how these are secured.
For IoT providers, this creates an obligation to transparently disclose security mechanisms and provide systems that can be maintained over the long term.
Exemplary RFID Readers for NIS2-Relevant Architectures
The selection of suitable RFID readers plays a central role in the context of NIS2. What is decisive here is not the mere reading function, but the ability to act as part of a controllable system architecture. Modern readers are increasingly taking on the functions of an IoT gateway and must be evaluated accordingly.
Kathrein RRU 4500 UHF RFID Reader
The RRU 4570 and the 45xx series from Kathrein Solutions exemplify the trend toward edge devices. The reader integrates a dual-core PC, multiple network interfaces, and mobile connectivity. It thus functions not only as a reader but also as part of the edge layer within an IoT architecture.
Support for EPC Gen2v2 also enables security features such as transponder-level authentication. Combined with network capabilities and local processing, the reader meets key requirements for NIS2-compliant systems.

Gen4 RFID Reader – RRU 45xx – ARU 35xx
Gen4 readers enable precise, efficient RFID for real-time IoT inventory and tracking.
FEIG LRU500i UHF RFID Reader
The LRU500i represents classic enterprise infrastructure. As an IP-based reader with PoE connectivity, it is designed to be integrated into central IT systems.
Unlike edge readers, the focus here is on stable communication and centralized control. For NIS2, it is crucial that such devices can be fully integrated into logging, monitoring, and access control systems.

ID LRU500i UHF Compact Reader
The ID LRU500i combines compact design with advanced UHF technology to optimize vehicle identification and parking access control in outdoor settings.
Balluff BIS VU-320 RFID System
Balluff systems are typically deeply integrated into production environments. They work closely with machine controllers and fieldbus systems and play a central role in OT processes.
In the NIS2 context, the challenge here lies in integrating these systems out of isolated automation into overarching security architectures. The devices themselves are robust and reliable, but their security is only achieved through integration via gateways and edge systems.
BLE–Wi-Fi Gateways as Security-Critical Transition Points
In addition to traditional RFID infrastructures, BLE-based systems are gaining increasing importance, particularly in the areas of asset tracking, RTLS, and condition monitoring. A typical architecture consists of battery-powered BLE tags that transmit their data to gateways, which in turn communicate with backend systems via Wi-Fi or Ethernet.
Technologies such as BluFi™ exemplify how this transition between local wireless communication and IP-based infrastructure is achieved. In this context, gateways play a central role as protocol translators and aggregation points. They connect not only different technologies but also security domains.
In the context of NIS2, these gateways are particularly critical. While BLE tags often offer only limited security mechanisms, the responsibility for authentication, data integrity, and secure forwarding lies with the gateway. It must ensure that only authorized devices are connected, that data cannot be manipulated, and that communication to the backend is secure.
At the same time, this creates a potential point of attack. If a gateway is compromised, this can enable access to a large number of end devices or allow manipulated data to be fed into central systems. Therefore, BLE–Wi-Fi gateways must be treated like traditional edge systems: with secure firmware, controlled access, network segmentation, and integration into monitoring and incident response processes.
Classification: Device vs. System
These examples clearly show that NIS2 relevance does not depend solely on the manufacturer or device type. The decisive factor is whether the reader:
can be addressed as a network device
can be integrated into monitoring and logging systems
is updatable and maintainable over the long term
is part of a segmented architecture
A simple USB reader does not meet these requirements. A network-enabled RFID reader, on the other hand, can—when used correctly—be a fully-fledged component of a secure IoT architecture.
Conclusion
The NIS2 Directive is leading to a structural realignment of cybersecurity. IoT systems are becoming a central component of regulatory requirements. Wireless technologies, edge components, and platforms must be conceived as an integrated security architecture. Secure, traceable, and consistently integrated systems are in demand.